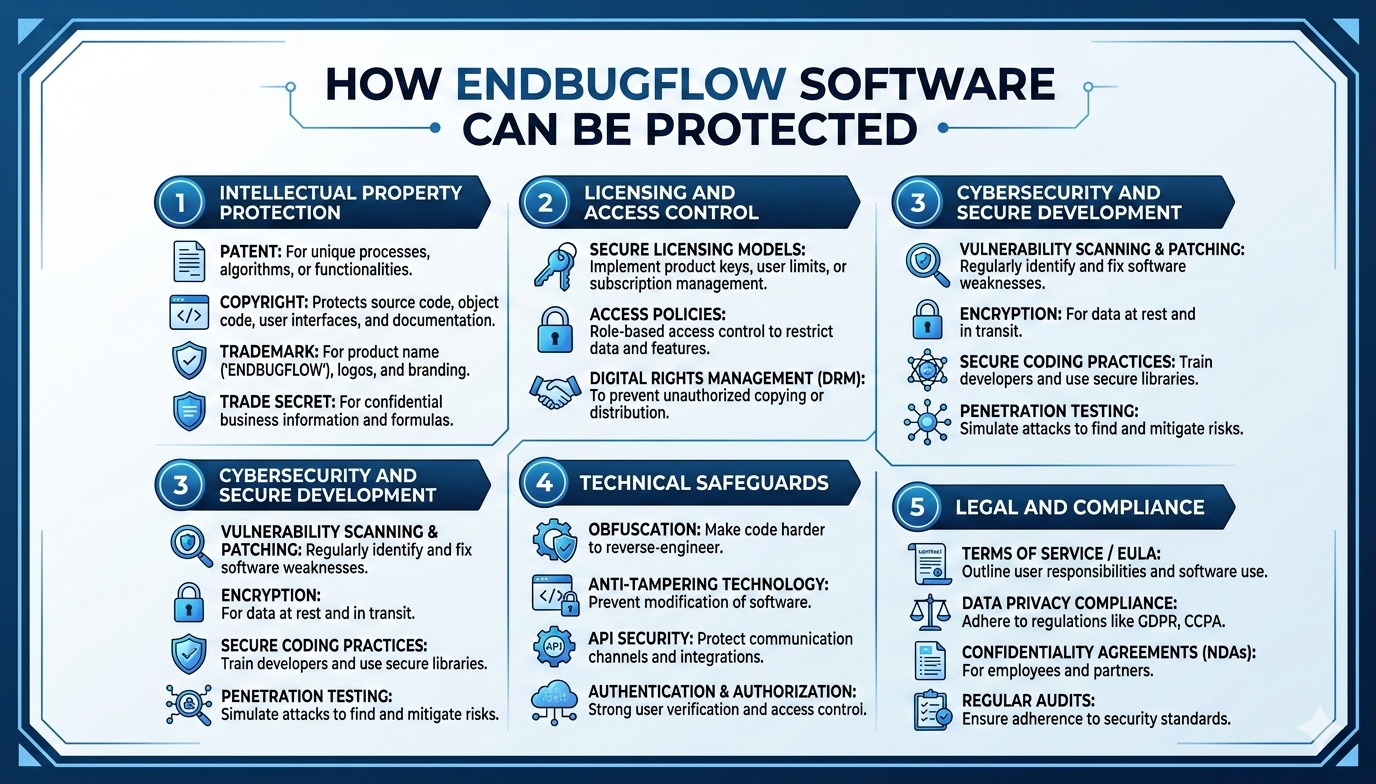
how endbugflow software can be protected: Complete Guide to Security, Compliance, and Risk Management
how endbugflow software can be protected, In today’s rapidly evolving digital ecosystem, software security has become a critical priority for organizations of every size. Businesses depend on applications to manage operations, store sensitive data, and deliver services to customers across the globe. With cyber threats growing in sophistication, companies must adopt a proactive and structured approach to defending their systems. This article provides a detailed discussion of how endbugflow software can be protected in modern environments, examining strategic planning, technical safeguards, organizational practices, and future trends that shape effective security frameworks.
The Importance of Software Protection
Software systems form the backbone of contemporary commerce, education, healthcare, and government services. Any vulnerability in an application can lead to data breaches, financial losses, operational downtime, and reputational damage. Attackers constantly search for weaknesses in code, infrastructure, or human processes. As a result, understanding how endbugflow software can be protected requires a layered and holistic approach rather than reliance on a single defensive mechanism.
Software protection is not merely about blocking unauthorized access. It involves preserving confidentiality, ensuring data integrity, and maintaining availability. Organizations must also guarantee compliance with legal and regulatory requirements. These goals demand coordinated action across development teams, IT administrators, leadership, and external partners.
Identifying Threats and Vulnerabilities
Before implementing protective measures, organizations must assess the potential risks facing their systems. Cyber threats can include malware attacks, phishing campaigns, insider threats, distributed denial-of-service attacks, and exploitation of unpatched vulnerabilities. A thorough risk assessment helps organizations evaluate how endbugflow software can be protected against both internal and external threats.
Key steps in vulnerability identification include:
- Conducting code reviews to detect security flaws.
- Running automated security scans.
- Performing penetration testing to simulate real-world attacks.
- Monitoring third-party libraries for known vulnerabilities.
By documenting weaknesses and prioritizing risks, companies can allocate resources efficiently and address critical issues first.
Secure Software Development Lifecycle (SSDLC)
One of the most effective strategies for long-term protection is embedding security into the development lifecycle. Instead of adding security features at the end of production, developers integrate them from the planning phase onward. Understanding how endbugflow software can be protected requires a commitment to secure design principles.
An SSDLC typically includes:
- Requirement Analysis – Define security requirements alongside functional goals.
- Secure Design – Incorporate encryption, authentication, and validation mechanisms from the start.
- Implementation – Write clean, secure code and follow best practices.
- Testing – Perform security testing at multiple stages.
- Deployment – Configure environments securely.
- Maintenance – Continuously patch and update software.
Developers must document how endbugflow software can be protected at the code level by applying practices such as input validation, proper error handling, and avoidance of hard-coded credentials.
Access Control and Identity Management
Controlling who can access software and what actions they can perform is fundamental to security. Unauthorized access is one of the leading causes of breaches. Organizations need clear policies defining how endbugflow software can be protected through identity governance and authentication frameworks.
Essential components of strong access control include:
- Role-Based Access Control (RBAC): Users are assigned permissions based on job roles.
- Multi-Factor Authentication (MFA): Requires multiple forms of verification.
- Least Privilege Principle: Users receive only the access necessary for their tasks.
- Regular Access Reviews: Periodic audits to remove unnecessary permissions.
Identity management systems should also log and track user activities. This not only deters malicious behavior but also aids forensic investigations if an incident occurs.
Encryption and Data Protection
Encryption is a powerful tool for safeguarding sensitive data. Whether data is stored in databases or transmitted across networks, it must be protected from interception and misuse. Another pillar of how endbugflow software can be protected involves encryption strategies at rest and in transit.
Key encryption practices include:
- Using strong encryption standards for stored data.
- Implementing secure communication protocols.
- Managing encryption keys carefully.
- Avoiding outdated cryptographic algorithms.
Beyond encryption, organizations should anonymize or tokenize sensitive data whenever possible. Minimizing the amount of stored sensitive information reduces potential exposure in case of a breach. how to update endbugflow software on pc
Network Security Measures
Software does not operate in isolation. It interacts with servers, databases, APIs, and client devices across networks. Organizations revisiting how endbugflow software can be protected should also segment networks and apply layered defenses.
Important network protection techniques include:
- Firewalls to filter incoming and outgoing traffic.
- Intrusion Detection and Prevention Systems (IDPS).
- Virtual Private Networks (VPNs) for secure remote access.
- Segmented network zones to limit lateral movement.
Network segmentation is particularly valuable in containing threats. If attackers breach one part of the system, segmentation prevents them from accessing critical components.
Application Monitoring and Incident Response
Even with robust preventive measures, no system is completely immune to threats. Continuous visibility strengthens how endbugflow software can be protected over time. Monitoring tools help detect unusual patterns, unauthorized access attempts, and performance anomalies.
Effective monitoring strategies involve:
- Real-time log analysis.
- Automated alerts for suspicious activity.
- Behavioral analytics to detect deviations from normal usage.
- Centralized security information and event management systems.
In addition, organizations must establish a clear incident response plan. This plan should outline roles, communication protocols, containment procedures, and recovery steps. Rapid response minimizes damage and reduces downtime.
Patch Management and Updates
Outdated software components are a major source of vulnerabilities. Attackers often exploit known flaws that have already been patched by vendors but not applied by users. Therefore, maintaining up-to-date systems is a critical part of protection strategies.
Patch management best practices include:
- Monitoring security advisories.
- Testing patches in staging environments.
- Automating updates when feasible.
- Keeping third-party libraries current.
Regular updates ensure that new security enhancements are integrated promptly, reducing the attack surface.
Regulatory Compliance and Legal Considerations
Compliance with laws and standards is essential for maintaining trust and avoiding penalties. Regulatory bodies in the United States often ask how endbugflow software can be protected under industry standards and privacy frameworks. These regulations may mandate encryption, audit logging, and breach notification procedures.
Organizations must stay informed about relevant regulations in their operating regions and industries. Compliance audits not only reduce legal risks but also strengthen overall security posture.
Employee Training and Security Awareness
Human error remains one of the most common causes of security breaches. Employees may fall victim to phishing emails, use weak passwords, or mishandle sensitive information. Training programs are vital for building a culture of security awareness.
Key elements of effective training include:
- Recognizing social engineering tactics.
- Creating strong and unique passwords.
- Reporting suspicious activity.
- Following secure data handling procedures.
When employees understand their role in protecting software, the organization becomes more resilient against threats.
Third-Party Risk Management
Many applications depend on external vendors, cloud providers, and open-source libraries. While these integrations enhance functionality, they also introduce new risks. Organizations must evaluate the security posture of third-party partners.
Strategies for managing third-party risk include:
- Conducting security assessments before onboarding vendors.
- Reviewing contractual security obligations.
- Monitoring vendor compliance continuously.
- Limiting third-party access to necessary resources.
A proactive approach reduces the likelihood that external weaknesses compromise internal systems.
Backup and Disaster Recovery Planning
Data loss can occur due to cyberattacks, hardware failures, or natural disasters. A comprehensive backup strategy ensures that organizations can recover quickly from disruptions.
Best practices for backup and recovery include:
- Maintaining multiple backup copies.
- Storing backups in geographically separate locations.
- Testing recovery procedures regularly.
- Automating backup processes.
Disaster recovery plans should outline recovery time objectives and communication protocols. Preparation ensures business continuity even in worst-case scenarios.
Cloud Security Considerations
As more applications move to cloud environments, security strategies must adapt. Cloud platforms provide scalability and flexibility but also require careful configuration.
Important cloud security measures include:
- Configuring secure storage permissions.
- Using identity and access management tools.
- Encrypting cloud data.
- Monitoring cloud activity logs.
Organizations must understand the shared responsibility model in cloud services, ensuring that both providers and customers fulfill their respective security roles.
DevSecOps Integration
Modern development practices emphasize rapid deployment and continuous integration. DevSecOps extends this model by embedding security into every phase of operations.
Benefits of DevSecOps include:
- Automated security testing in CI/CD pipelines.
- Immediate identification of vulnerabilities.
- Improved collaboration between security and development teams.
- Faster remediation of discovered issues.
This approach fosters a proactive mindset, making security an integral part of innovation rather than a bottleneck.
Future Trends in Software Protection
Technology continues to evolve, bringing new opportunities and new risks. Emerging technologies will reshape how endbugflow software can be protected in the years ahead. Artificial intelligence, machine learning, and advanced analytics are already being used to detect anomalies and predict threats.
Future trends may include:
- Zero-trust architectures.
- Behavioral biometrics for authentication.
- Automated threat hunting.
- Quantum-resistant cryptography.
Organizations that embrace innovation while maintaining disciplined security practices will be better positioned to defend their systems against evolving challenges.
Building a Security-First Culture
Technical measures alone cannot guarantee safety. Leadership must promote a security-first mindset throughout the organization. This involves allocating sufficient budgets, setting clear policies, and encouraging accountability.
A security-first culture includes:
- Transparent reporting channels.
- Continuous improvement initiatives.
- Regular audits and assessments.
- Recognition of secure development practices.
When security becomes a shared responsibility, resilience increases significantly.
Conclusion
Protecting modern software requires a comprehensive and evolving strategy. From secure development and encryption to access control, monitoring, and regulatory compliance, organizations must adopt a layered defense model. By prioritizing risk assessment, employee education, third-party management, and technological innovation, companies can significantly reduce vulnerabilities.
Long-term protection depends on vigilance, adaptability, and collaboration across teams. By implementing best practices and maintaining a forward-looking approach, organizations can safeguard their applications, data, and reputation in an increasingly complex digital landscape.